In 2025, as cloud adoption reaches record highs, U.S. businesses face a dual-edged sword: unparalleled flexibility and scalability on the one hand, and rapidly evolving security risks on the other. With sensitive data flowing into cloud environments and workforces distributed across remote and hybrid settings, securing cloud usage has become a mission-critical priority. Enter the Cloud Access Security Broker (CASB)—an essential component in a modern cybersecurity strategy designed to detect threats, enforce compliance, and give businesses the confidence to innovate without compromising their security posture.
Table of Contents
What Is a Cloud Access Security Broker (CASB)?
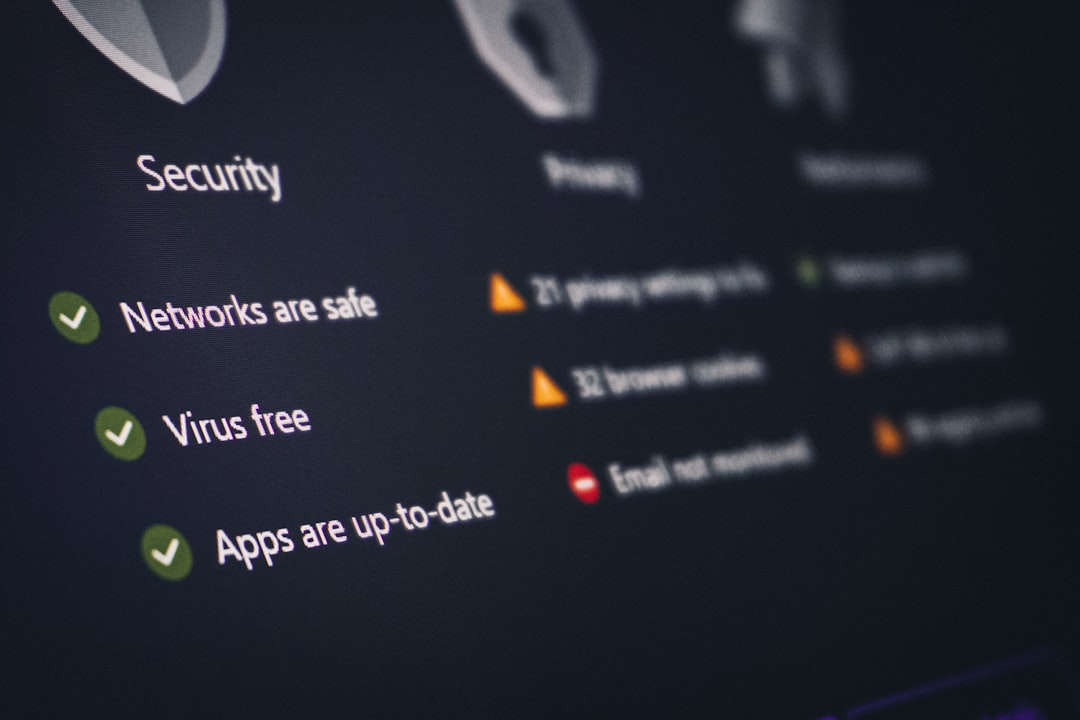
A Cloud Access Security Broker is a security solution deployed either on-premises or in the cloud, positioned strategically between users and cloud service providers. Its role is to monitor data traffic, enforce policies, and intercept malicious behavior before it causes harm. In essence, CASBs serve as control points to help organizations extend their security guidelines to cloud applications that might otherwise operate without rigorous oversight.
The emergence of CASB software in the past decade has accelerated due to increased reliance on Software-as-a-Service (SaaS) tools like Google Workspace, Microsoft 365, Salesforce, and Dropbox. In 2025, the technology continues to evolve, integrating machine learning and advanced analytics to deliver proactive threat detection and precise data governance.

Why U.S. Businesses Need CASBs in 2025
Today’s rapidly shifting threat landscape makes traditional perimeter-based security models obsolete. U.S. businesses face regulatory scrutiny, data breaches, insider threats, and the challenges of managing multiple cloud platforms. CASBs address these concerns head-on by offering:
- Visibility: Identify and inventory all cloud apps in use across the organization, including shadow IT.
- Data Security: Apply granular controls to sensitive data, preventing leakage and ensuring encryption.
- Threat Protection: Detect anomalous behavior, malware infiltration, and risks stemming from third-party integrations.
- Compliance Management: Enforce enterprise compliance policies associated with HIPAA, GDPR, FedRAMP, CCPA, and more.
With tighter regulatory oversight in 2025 and increasing penalties for mishandling customer data, implementing a CASB solution isn’t just a recommendation—it’s a necessity for U.S. businesses of all sizes.
Key Features to Look For in CASB Solutions
Not all CASB tools are created equal. The effectiveness of your CASB depends on the breadth and depth of its capabilities. When evaluating CASB software, look for features such as:
1. Cloud Discovery
This feature automatically detects what cloud services are accessed across your network, offering visibility into unsanctioned apps, a common source of data leakage.
2. Data Loss Prevention (DLP)
Enterprise-grade DLP mechanisms identify, monitor, and protect sensitive data moving to and from cloud apps. This includes PII, PHI, and intellectual property.
3. Encryption and Tokenization
Modern CASB tools apply encryption techniques to protect sensitive data without affecting functionality. Tokenization replaces sensitive data with non-sensitive equivalents when stored.
4. User and Entity Behavior Analytics (UEBA)
By analyzing usage patterns, UEBA identifies suspicious activities such as credential stuffing, privilege abuse, or unusual access times.
5. Risk Scoring and Threat Intelligence
Risk engines rate app and user-level risks, offering administrators insights into event severity while integrating threat intelligence feeds for proactive defense.
6. API Integration with Cloud Services
Direct API access enables deeper visibility into cloud apps and facilitates control over data at rest—something traditional security tools cannot achieve.

Leading CASB Vendors in 2025
The CASB market is saturated with a variety of enterprise choices. Here’s a quick look at the leading providers that U.S. businesses are turning to in 2025:
- Microsoft Defender for Cloud Apps: Ideal for businesses invested in Microsoft ecosystems, offering native integration, strong analytics, and robust compliance tools.
- McAfee MVISION Cloud: Comprehensive DLP, UEBA, and real-time protection for a wide range of SaaS, IaaS, and PaaS environments.
- Netskope Security Cloud: A leader in real-time risk analysis and advanced machine learning capabilities, suitable for large enterprises.
- Bitglass (Forcepoint ONE): A user-friendly interface with powerful data protection and high performance across remote endpoints.
- Palo Alto Networks Prisma Access: An integrated security solution offering cloud-delivered CASB with Zero Trust capabilities.
Each of these vendors offers unique capabilities tailored to different use cases and industries. When choosing a CASB, always align features with your business’s specific risks and regulatory requirements.
Deployment Models: Choosing the Right Fit
CASBs can be deployed in several ways, and understanding these models is crucial for aligning with your IT environment.
1. API-Based Deployment:
Quick to set up and low in latency, this model uses cloud service APIs for data visibility and control. However, it’s limited to sanctioned apps.
2. Proxy-Based Deployment:
This model intercepts user traffic in real-time for fine-grained control. While powerful, it may introduce latency and complexity in configuration.
3. Hybrid Deployment:
This combines the strengths of API and proxy models, offering deep visibility and control with the flexibility to cover both sanctioned and unsanctioned services.
Each method has trade-offs. Businesses seeking broader protection across on-prem and SaaS environments often prefer hybrid configurations.
Best Practices for Implementing CASB Solutions
Successful CASB implementation not only depends on technology, but also on the strategy and governance around it. Here are best practices that can help ensure a smooth rollout:
- Conduct a cloud risk assessment: Understand which applications your organization is using and which present the highest risk.
- Involve key stakeholders: Security, IT, compliance, and business units should work collaboratively to align on goals.
- Set clear security policies: Define what constitutes acceptable versus risky cloud usage and enforce this with automation.
- Train employees: Ensure users understand safe cloud usage practices as well as the consequences of bypassing guidelines.
- Monitor and adjust: Use reports and analytics provided by the CASB platform to refine policies and update threat detection logic continuously.
The Future of CASB in a Zero Trust World
With Zero Trust architectures becoming the new standard in 2025, CASBs are evolving to better align with identity-driven access and continuous verification models. Forward-thinking vendors are integrating CASB capabilities into Secure Access Service Edge (SASE) frameworks, delivering security wherever the user is located—without relying on outdated perimeter-based models.
In the near future, we can expect CASB solutions to further integrate with AI-driven automation, autonomous behavioral analytics, and quantum-resistant encryption for ultra-high security environments. These advances will not only reduce response times but also offer predictive insights to stop threats before they materialize.
Conclusion
The push to the cloud is irreversible, and cyber threats are evolving faster than ever. For U.S. businesses seeking to thrive in this landscape, Cloud Access Security Broker software represents more than just a security tool—it’s a strategic enabler of digital transformation. By choosing the right CASB solution and implementing it with thoughtful governance, organizations can protect their data, earn client trust, and confidently embrace the future of work.
In 2025, data protection isn’t optional. It’s the foundation of competitive advantage—and CASBs lead the charge.