Cloud security used to feel like trying to guard a castle made of fog. Everything moves. New servers spin up in seconds. Containers appear and disappear. One small mistake can leave the door wide open. That is why Cloud Security Posture Management (CSPM) tools are now a must-have. They scan your cloud environment and flag risky misconfigurations fast. Some, like Wiz, made this approach famous. But they are not alone.
TLDR: Cloud misconfigurations are one of the biggest causes of data breaches. CSPM platforms scan your cloud setup and alert you to risks within minutes. Tools like Orca Security, Prisma Cloud, Lacework, Check Point CloudGuard, and Trend Micro Cloud One offer strong alternatives to Wiz. They make cloud security simpler, faster, and far less stressful.
Let’s break it down in plain English. No buzzword soup. Just simple ideas.
Table of Contents
What Is Cloud Security Posture Management?
Imagine your cloud environment as a huge digital warehouse. Inside are apps, databases, storage buckets, user accounts, APIs, and more. Each one has settings. If those settings are wrong, you may accidentally expose sensitive data to the internet.
That is called a misconfiguration.
Examples?
- An Amazon S3 bucket set to public.
- An admin account without multi-factor authentication.
- An open port that should be closed.
- A database with weak access controls.
CSPM tools continuously scan for these problems. They compare your setup against security best practices. Then they alert you. Some even fix the issue automatically.
Simple idea. Big impact.
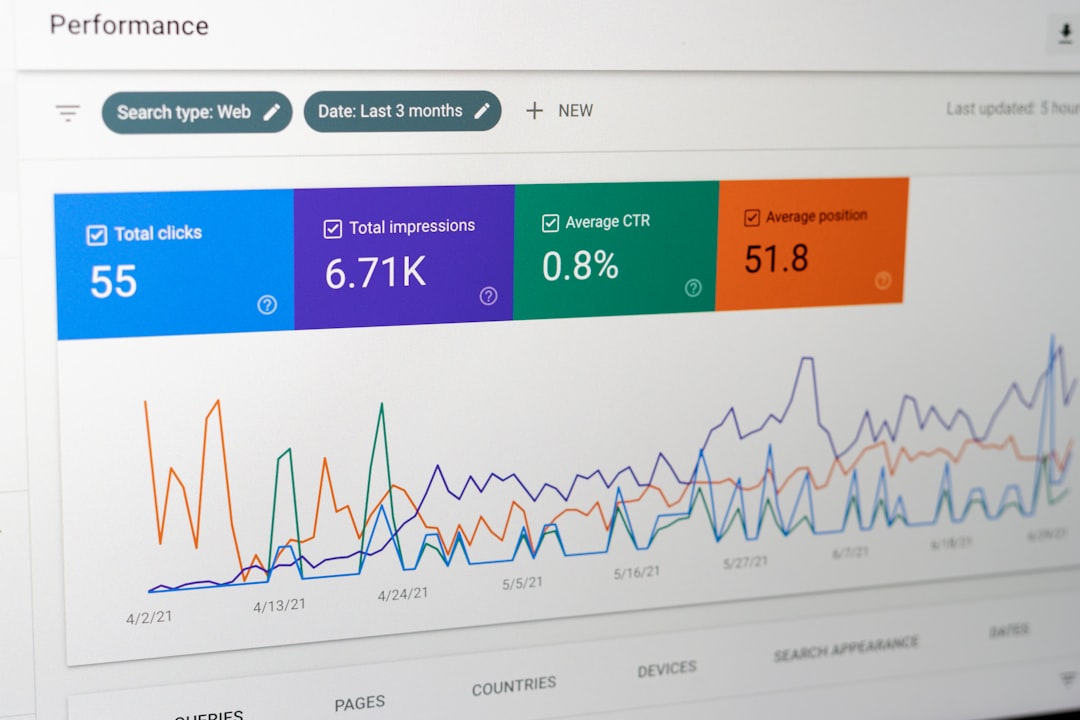
Image not found in postmetaWhy Detecting Misconfigurations in Minutes Matters
Speed is everything in cloud security.
A misconfiguration can be exploited in minutes. Attackers use bots that scan the internet non-stop. They are not guessing. They are actively hunting for mistakes.
The faster you detect an issue, the less damage it causes.
Modern CSPM tools:
- Scan continuously, not once a week.
- Prioritize risks based on severity.
- Show how issues are connected.
- Reduce alert noise.
Now let’s explore five powerful platforms that do this well.
1. Orca Security
Orca Security is often mentioned alongside Wiz. For good reason.
Its biggest strength? Agentless scanning. You do not need to install software on every workload. Orca connects directly to your cloud provider through secure APIs.
That makes deployment fast. Sometimes within hours.
What makes Orca stand out?
- Deep visibility into AWS, Azure, and Google Cloud.
- Risk-based prioritization.
- Side-scanning technology that inspects workloads without disruption.
- Strong compliance reporting.
Orca also maps attack paths. It helps you see how a small issue could turn into a major breach. That context is powerful. It helps security teams focus on what truly matters.
It is a solid Wiz alternative for companies that want quick setup and minimal operational overhead.
2. Prisma Cloud by Palo Alto Networks
Prisma Cloud is a big name in cloud security. It goes beyond CSPM. It offers a full Cloud Native Application Protection Platform, also called CNAPP.
That means it combines:
- CSPM
- Container security
- Infrastructure as Code scanning
- Runtime protection
Prisma Cloud excels in multi-cloud environments. If your company runs on AWS, Azure, and Google Cloud at the same time, Prisma gives centralized visibility.
Its key strengths:
- Broad compliance coverage.
- Strong integration with DevOps pipelines.
- Detailed risk insights.
- Advanced threat detection.
The platform can feel complex at first. But once configured, it delivers deep insights very quickly. Misconfigurations are flagged in near real time.
This tool works well for larger enterprises with complex environments.
3. Lacework
Lacework focuses heavily on behavior and automation.
Instead of only scanning static settings, it also watches how systems behave. This helps detect unusual activity that may signal compromise.
Its Polygraph technology maps relationships between cloud resources, users, and workloads. That means fewer false positives.
Why teams like Lacework:
- Automated anomaly detection.
- Clear visual dashboards.
- Lightweight deployment.
- Strong support for Kubernetes.
Lacework is especially helpful for fast-growing companies. Startups love it. It scales well. And it reduces the burden on small security teams.
Misconfigurations are detected fast. But more importantly, they are explained clearly. No cryptic error messages.

4. Check Point CloudGuard
Check Point is a long-time cybersecurity player. CloudGuard is its answer to modern cloud complexity.
CloudGuard offers strong CSPM capabilities along with:
- Threat prevention
- Workload protection
- Network security
It shines in hybrid environments. If you run both on-premises systems and cloud workloads, CloudGuard connects them smoothly.
Top features include:
- Automated misconfiguration detection.
- Built-in compliance templates.
- Real-time risk assessment.
- Strong identity and access analysis.
One strength is its focus on preventing lateral movement. If an attacker enters your cloud, CloudGuard helps stop them from spreading.
It is a dependable option for organizations that already use Check Point firewalls or security tools.
5. Trend Micro Cloud One – Conformity
Trend Micro has been in security for decades. Its Cloud One platform includes a service called Conformity, which focuses on CSPM.
It continuously scans cloud accounts for dangerous settings. The system checks against thousands of rules and best practices.
Why consider Trend Micro Cloud One?
- User-friendly interface.
- Strong compliance monitoring.
- Clear remediation guidance.
- Automated alerts.
One nice touch is its actionable advice. It does not just say, “This is wrong.” It tells you how to fix it step by step.
For teams that want clarity without complexity, it is a strong contender.
What To Look For in a CSPM Platform
Not every tool fits every company. Before choosing, ask a few simple questions.
- Do you run single-cloud or multi-cloud?
- Do you need agentless deployment?
- How important is compliance reporting?
- Do you want DevSecOps integrations?
- Is your team small or large?
Also look for:
- Risk prioritization. Not all issues are equal.
- Attack path analysis. Context matters.
- Low false positives. Alert fatigue is real.
- Automation. Fix problems fast.
The best tools save time. They reduce noise. They make security manageable.
Common Cloud Misconfigurations These Tools Catch
You might be surprised how common these are.
- Public storage buckets.
- Unencrypted databases.
- Overly permissive IAM roles.
- Disabled logging.
- Open SSH or RDP ports.
- Missing MFA for privileged users.
Many breaches start with something simple. Not advanced hacking. Just a forgotten setting.
That is what makes CSPM so powerful. It focuses on the basics. And the basics matter.
The Future of Cloud Security Posture Management
CSPM is evolving fast.
Today, platforms are moving toward full CNAPP solutions. That means combining posture management, workload protection, identity security, and runtime defense into one platform.
Artificial intelligence is also playing a bigger role. Tools now:
- Predict risk patterns.
- Auto-prioritize threats.
- Suggest fixes intelligently.
The goal is simple. Less manual work. More accurate protection.
Cloud environments will only grow more complex. More containers. More microservices. More APIs.
Security teams need tools that keep up.
Final Thoughts
Cloud misconfigurations are silent risks. They do not make noise. They do not crash systems. They just wait quietly for someone to notice.
Or exploit them.
That is why tools like Wiz became popular so quickly. They bring visibility. They bring speed. They turn confusion into clarity.
But Wiz is not your only option.
Orca Security offers deep visibility without agents.
Prisma Cloud delivers enterprise-level breadth.
Lacework blends automation with behavior analysis.
Check Point CloudGuard strengthens hybrid defenses.
Trend Micro Cloud One provides clarity and simplicity.
All of them detect misconfigurations in minutes. All of them reduce risk. And all of them make cloud security feel less overwhelming.
At the end of the day, cloud security does not have to be scary. With the right CSPM platform, it becomes structured. Manageable. Predictable.
And that makes all the difference.