Modern applications are increasingly built using microservices—small, independent services that communicate over networks to deliver complex functionality. While this architectural style provides flexibility and scalability, it also introduces significant challenges in managing traffic, ensuring reliability, and enforcing security. This is where service mesh tools like Istio step in, offering a dedicated infrastructure layer that manages service-to-service communication in a transparent, controlled, and observable way.
TLDR: Service mesh tools like Istio help organizations manage, secure, and monitor communication between microservices without changing application code. They provide features such as traffic routing, load balancing, encryption, authentication, and observability. By abstracting networking concerns away from developers, service meshes improve reliability and security in complex distributed systems. However, they also add operational complexity and require careful planning before adoption.
As microservices proliferate across cloud-native environments, Kubernetes clusters, and hybrid infrastructures, traditional networking approaches become insufficient. Each service may need to talk to dozens of others, and manually configuring traffic rules, retries, timeouts, and encryption quickly becomes unmanageable. A service mesh addresses these challenges by introducing a dedicated communication layer that handles these cross-cutting concerns systematically and at scale.
Table of Contents
What Is a Service Mesh?
A service mesh is a configurable infrastructure layer for managing service-to-service communication in a distributed system. Instead of embedding networking logic directly into application code, a service mesh abstracts these responsibilities into a separate layer.
The architecture typically consists of two major components:
- Data Plane: Lightweight proxies (often Envoy) deployed alongside each service instance, usually as sidecar containers.
- Control Plane: A centralized management component that configures and coordinates the proxies.
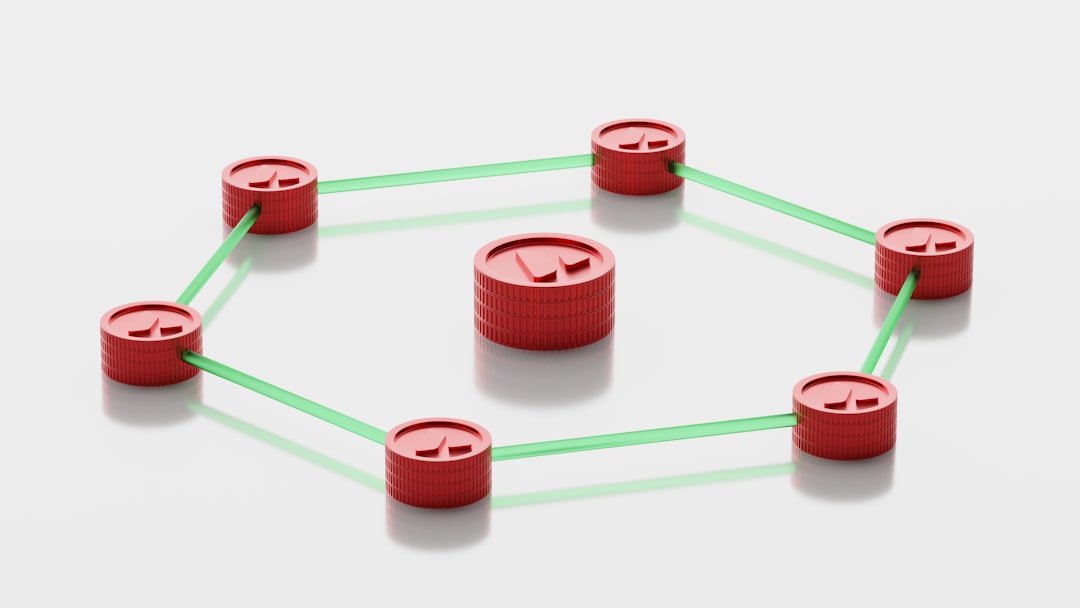
The data plane intercepts and manages all inbound and outbound service traffic. The control plane enforces policies, collects telemetry, and distributes routing rules. In the case of Istio, the control plane configures Envoy sidecars to handle advanced traffic behaviors without the application even being aware of it.
How Istio Fits Into the Picture
Istio is one of the most mature and widely adopted service mesh platforms. Built originally by Google, IBM, and Lyft, Istio integrates deeply with Kubernetes and leverages Envoy as its data plane proxy.
Istio provides:
- Advanced traffic management
- Built-in security and encryption
- Comprehensive observability
- Policy enforcement and access control
What makes Istio particularly compelling is its ability to implement these features without requiring developers to modify application code. This separation of concerns allows development teams to focus on business logic while operations teams manage networking and security declaratively.
Traffic Management: Control at Layer 7
In a distributed microservices environment, controlling traffic flow is essential for reliability and resilience. Istio operates at Layer 7 (application layer), enabling fine-grained routing rules based on headers, paths, and other metadata.
Key traffic management capabilities include:
- Intelligent routing: Direct traffic based on request attributes (e.g., send 10% of requests to a new version).
- Canary deployments: Gradually roll out updates and test new versions safely.
- A/B testing: Route users to different service versions for experimentation.
- Retries and timeouts: Automatically retry failed requests and set request deadlines.
- Circuit breaking: Prevent cascading failures when downstream services become unavailable.
For example, if a new version of a payment service is deployed, Istio can direct a small percentage of users to the updated version. If errors increase, traffic can be switched back instantly—without redeploying services.
Image not found in postmetaThis ability to transparently manage traffic flow significantly improves system resilience and enables safer continuous delivery practices.
Security: Zero-Trust by Default
Security in microservices architectures is inherently complex. With dozens or hundreds of services communicating internally, ensuring encrypted, authenticated communication is critical. Service meshes like Istio embrace a zero-trust security model.
Istio’s key security features include:
- Mutual TLS (mTLS): Automatic encryption of service-to-service communication.
- Strong identity: Each service is assigned a cryptographic identity.
- Authentication policies: Define which services are allowed to communicate.
- Authorization rules: Fine-grained access control policies.
With mTLS enabled, every communication between services is encrypted and verified. This ensures that even if an attacker gains internal network access, they cannot easily impersonate services or intercept sensitive data.
Importantly, Istio can automatically issue and rotate certificates, reducing operational risk. Security policies are applied centrally via configuration rather than embedded in application code, making compliance and auditing more manageable.
Observability: Seeing Inside the Mesh
One of the greatest challenges in microservices environments is observability—understanding what’s happening across dozens of distributed components. Istio enhances visibility by collecting rich telemetry from every service-to-service interaction.
Out-of-the-box observability features include:
- Metrics: Request rates, error rates, latency distribution.
- Distributed tracing: Track requests as they propagate across services.
- Access logs: Detailed records of traffic behavior.
These insights allow teams to identify bottlenecks, diagnose performance issues, and trace failures across service chains. Integrated dashboards, often paired with tools like Prometheus, Grafana, and Jaeger, provide near real-time visibility into system health.
Without a service mesh, implementing such observability would require manual instrumentation in every service. Istio centralizes data collection within its sidecar proxies, ensuring consistent metrics without code changes.
Policy and Governance
Beyond traffic and security, service meshes enable centralized policy enforcement. Organizations can define rules governing:
- Rate limiting
- Quota management
- Access restrictions
- Compliance requirements
This centralized approach strengthens governance, especially in regulated industries. Instead of relying on individual teams to implement security policies correctly, administrators can enforce them mesh-wide. Policies become declarative configurations rather than scattered code fragments.
Benefits of Using Istio and Service Mesh Tools
Adopting a service mesh provides numerous advantages in complex environments:
- Developer productivity: Developers don’t have to build networking and security features from scratch.
- Operational consistency: Standardized communication patterns across services.
- Improved resilience: Built-in retries, circuit breakers, and failover logic.
- Enhanced security posture: Automatic encryption and identity management.
- Scalable observability: Unified metrics and tracing.
For organizations deploying dozens or hundreds of services, these benefits translate into faster release cycles, improved uptime, and more predictable performance.
Challenges and Considerations
Despite its powerful capabilities, Istio is not a silver bullet. Implementing a service mesh introduces:
- Operational complexity: Additional infrastructure components to manage.
- Resource overhead: Sidecar proxies consume CPU and memory.
- Learning curve: Teams must understand new configuration concepts.
- Troubleshooting difficulty: More layers can complicate debugging.
For smaller systems with limited services, the overhead may outweigh the benefits. Organizations should evaluate:
- The number of services deployed
- Security and compliance requirements
- Traffic complexity
- Operational maturity
In some cases, lighter service mesh alternatives or managed solutions may be more appropriate.
Istio in Cloud-Native Ecosystems
Istio integrates deeply with Kubernetes, making it especially suited for cloud-native deployments. Kubernetes handles container orchestration, while Istio manages how those containers communicate. Together, they form a powerful platform for scalable distributed applications.
In multi-cluster and multi-cloud setups, Istio can provide consistent traffic policies and security configurations across environments. This capability is increasingly important as organizations adopt hybrid cloud strategies.
Moreover, Istio supports ingress and egress traffic management, controlling how external users access services and how services communicate with external APIs. This unified model reduces fragmentation in networking configurations.
The Future of Service Mesh
As distributed systems grow in complexity, service meshes are evolving to be lighter, more modular, and more performance-efficient. Innovations like ambient mesh architectures aim to reduce sidecar overhead while preserving core features.
Emerging trends include:
- Integration with serverless platforms
- Improved multi-cluster federation
- Enhanced policy management with declarative APIs
- Stronger alignment with zero-trust security frameworks
Service meshes are increasingly seen not just as networking tools, but as foundational components of secure, resilient cloud platforms.
Conclusion
Service mesh tools like Istio play a pivotal role in managing the complexity of modern microservices environments. By offloading traffic control, security enforcement, and observability to a dedicated infrastructure layer, they allow teams to scale distributed systems with confidence.
While adoption requires careful planning and operational discipline, the benefits—fine-grained traffic management, automatic encryption, centralized policy enforcement, and deep system visibility—are transformative for large-scale deployments. As organizations continue embracing microservices and cloud-native architectures, service meshes are poised to remain a cornerstone of secure and reliable service communication.
In a world where applications are no longer monoliths but interconnected ecosystems of services, tools like Istio ensure that those connections remain intelligent, observable, and secure.