How much does a cyber-security error cost?
- Business reputation
- Financial loss
- Shut Down of business
In this digital era, cyber-security is necessary if you are a web owner, so never make the blunder of considering it an option. Some site owners focus on multiple factors like products, conversions, sales, customer satisfaction, etc., but miss out on protecting their digital web.
On the other hand, few owners aware of cyber-security invest in the same but miss out on simple cyber-security mistakes, which costs them a fortune.
Furthermore, research indicates that nine of the ten breaches (86%) were focused on gaining money. So, you won’t be surprised if I say that when small cyber-security mistakes are prevented, you can easily avoid significant cyber-attacks and their losses. According to Payforessaycheap, students are especially vulnerable to many kinds of cyberattacks like frauds, identity thefts, and all sorts of online harassment.
This article will discuss some cyber-security mistakes made by tech-savvy experts and business owners and their best possible solutions.
Table of Contents
1. Company Failure to Identify Employees as Threats
An IBM study indicates that human error is responsible for 95% of security breaches. You can pinpoint that factor to lack of employee training. Thus, if the employees cannot identify phishing emails or malicious software and tend to click or download the same, it may cause disaster. Common botches are the use of public Wi-Fi or plugging in non-trustworthy devices.
Moreover, unattended computers can be compromised easily, so it’s better to keep them password protected for data safety. Apart from that, passwords written on notepads or accesses shared by colleagues can be dangerous for your business.
These internal threats can be intentional (34%) too. However, few internal threat indicators are:
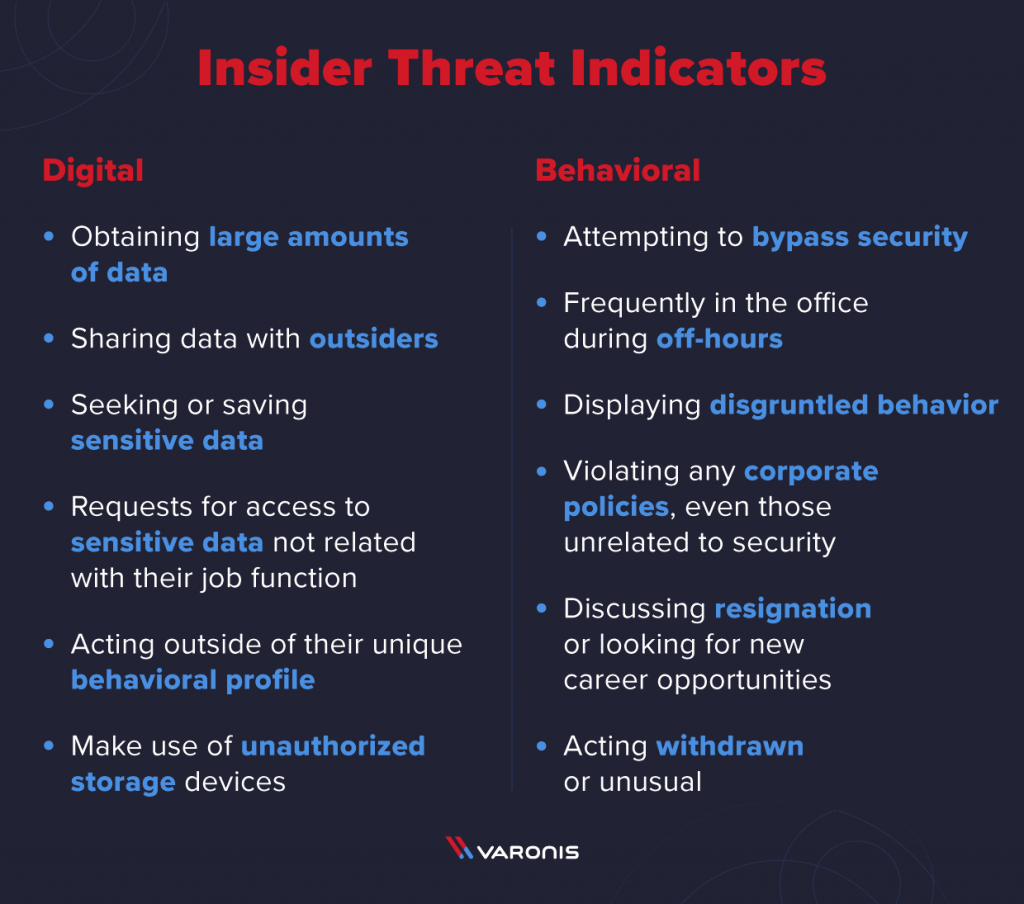
Example: Ex-employee of SunTrust Bank had stolen 1.5 million client’s data.
Solution:
Training on cyber-security awareness regularly can help prevent employees from opening unknown attachments, visiting unknown sites, or downloading unknown software.
In addition, stringent company policies should be made, which should be shared amongst all employees. Moreover, employees should take mock tests to see how many employees take the bait and regularly increase awareness. In stricter policies, employees should be held liable for the damages.
2. Allowing Weak Credentials

The convenience of setting a standard password for all the user accounts sounds good, however, not only to the IT department but also to hackers. The leakage of passwords in one account can pave the way for hackers to access your entire system or digital infrastructure. Moreover, Verizon Study indicates that a whopping 81% of the security breaches are weak passwords.
Basic credentials which are also the culprits:
- Common passwords, like name, DOB, etc
- Using the same password in all accounts
- Sharing of passwords
Solution:
- Use the Password Manager tool by Google, which checks the strength of your password
- Alphabet + number + upper case alphabet + lower case alphabet + special character + symbol = Strong Password. A long password, including MFA (multi-factor authentication), is ideal for securing your digital business
- Ensure that the same passwords are not repeated, not on public display, and are not shared internally amongst employees. Use unique passwords for different accounts and ensure that they are encrypted for solid security
- Define the password expiry dates so that the same is compulsorily changed
3. Weak or Non-Existent Information Security Policies

The IT department’s security policies should be robust, defined, and consistent with the management team. It should also be addressed as a business issue and should cover the security objectives, access controls, data privacy, web security, security awareness, etc.
Few policies include:
- Policy on Data Privacy: How should the new data be added, accessed, secured, and stored to prevent data loss or leakage should be clearly stated in the policy
- Workplace Theft Policy: Laptop theft can be prevented by ensuring that they are not left unattended. This, in turn, shields misuse of data too. The policy should also state the employee’s liability for the misuse or theft of their allotted laptop
- Policy on Social Media: Content that can and cannot be posted on social media should be clarified. Even policy on using the best of social media to prevent cyber-threats and malware should be specified
- Data Disposal Policy: Policy on how to shred old data and dispose of it securely should be specifically mentioned to prevent data misuse
4. Using Weak Encryption

Most business owners are aware of encryption security and hence utilize it to secure their digital business. But they are unaware that weak encryption is as good as no encryption when dealing with sophisticated and tech-savvy hackers.
Example: Some web owners opt for disk encryption which starts by switching off the server. Once the server is in active mode, data starts getting decrypted and accessible to the bad guys
Encryption Security Vulnerabilities Are Inclusive of:
- Unencrypted emails or storage of data
- Employees working at remote places
- Data communicated in plain text
- Not using MFA
- Not using BYOD (bring your device) policy
Many encryption certificates are called SSL (Secure Socket Layer) certificates, which provide 256-bit solid encryption to browser-server data communications when installed on the website.
The best global SSL brands like Comodo SSL certificate, RapidSSL, DigiCert, Thawte, GeoTrust, and more at discounted prices are available at CheapSSLShop, a trustworthy SSL certificate provider. So visit the store and grab one today to avoid the biggest cyber-security mistake.
5. Relying Strictly on ISP for Security

ISP (Internet Service Provider) security is essential, but relying entirely on it for your business security is a grave mistake. It may protect against external threats to some extent but may fail to defend against internal threats.
Your company requires multi-layered security, which secures all your gateways and endpoints against both types of threats. Using anti-virus software, firewalls, SSL certificates, internet gateways, etc., should be included in the security measures.
Software patching prevents 60% of breaches if they are updated regularly.
6. Failure to Test Your Security

Though you may be well-equipped with the latest security hacks to protect your website, you need to test the same to fix open gateways. Though many business owners do security testing, it may not be sufficient to identify potential blemishes.
Adversaries think the same way you do and hence can launch successful attacks. Still, if your security systems are tested and updated, it may prevent most cyber threats.
Therefore, ensure that your security perimeter is expanded to all the defense lines from the first line to the endpoints. With diverse adversaries, it’s time to diversify your testing criteria to outmaneuver their motives for your business safety.
Security testing tools like Zed Attack Proxy (ZAP), Wfuzz, Wapiti, etc., are some popular ones that may fulfill your requirement.
7. Using Insecure Wi-Fi

Public places like airports, cafes, coffee shops, etc., provide accessible Wi-Fi facilities to their customers. However, many locals forget that these accessible unsecured networks are gateways to MIM (man-in-middle) attacks, unencrypted networks, malware, snooping, etc. So they share sensitive information on these malicious hotspots only to regret it later.
Ensure that your internal staff always use VPN (Virtual Private Network) even while transacting from these public places to maintain sensitive data security. The VPN type can be OS-specific, such as a VPN for Windows, or a general VPN.
Final Thoughts
The alarming figures of cyber-attacks have resulted in raising awareness in the digital community.
Since the exploits focus on system vulnerabilities, to penetrate networks, you need to be vigilant at all times, have a plan B in case of contingency, update your systems regularly, and use SSL encryption security to prevent them from entering your network gateway. Good luck!